Jul 26, 2021
Posted in blog, Information Security, Malware, mobile, security awareness
I have had this question come up quite a lot from people asking “hey, how would I know if my phone is hacked, it has been doing some weird things”.
So here is a list of items you should check to assess if your mobile phone might be compromised.
What might show my phone got hacked ?
Check Your Data Usage
Most mobile devices will let you check how much data each app has used up. For apps related to social media it would make sense for them to use up a lot of data. But if you have an app, you barely use, and you can see there is quite a lot of data usage on it. That might indicate that it has been running and sending/receiving data. Compromised apps, may tend to use more data since the attacker may be trying to send data over your phone to their own systems. A good way to measure this is to check your app data usage every month. So, you get to know what the average data usage if for each app you use.
Pop ups or Ads
This one is an obvious one, if you see random ads popping up out of no where. Or random windows pop up on your screen. There is a good chance your phone has malware, and/or an app was installed and could have full access to your mobile device. You should go through ALL your apps to see what you have running on your mobile device. If there is anything that you see which should not be running or installed. Remove the app and check to be sure it was removed with the app no longer showing up as running/installed.
Your Phone gets hot all the time
A phone gets very hot to touch when it’s running an app that takes up a lot of processing power. And, that makes your phone start to heat up. If this is happening to a point where your phone is always super hot to touch. Then chances are a malicious app is running all the time causing your phone to heat up. This is a good chance to view all apps running and see which one has been running the most. It could be an indicator that it is a malicious app and should be removed.
How did I get hacked ?
READ MORE OF THIS POST
Dec 6, 2019
Posted in blog, Encryption, Featured, Information Security, pen testing, security awareness, Windows
Stealing Windows Wi-Fi WPA2-PSK Passwords through PowerShell
This week, I was hanging out with a friends, who happened to
forget their Wi-Fi Password to connect a new device to their network. I
decided, I would find a way and help them out so they could obtain the Wi-Fi
password. It then led me to a thought, that a malicious attacker could
technically use the same technique. Or, that it could be a good technique used
when pen testing an environment. So, therefore, I have decided to make a blog
post about it. Enjoy!
Read more Of This Post!
May 22, 2017
Posted in blog, Encryption, Information Security, The Internet Of Things
Network Security for IP Camera’s & Video Surveillance Systems
These days many devices have some form of interaction with our networking devices and the internet itself! What people forget is much like our desktops, laptops and mobile devices. All of these other types of devices need to be secured. The average person is going to assume no security is needed and that the product itself is already fairly secure by default. In my personally opinion, I’d say the default security settings are usually not sufficient enough to keep the device and your network safe.
I’ve created a guide below of procedures that can be followed to enhance the security measures for your IP Camera’s and systems.
IP Camera Hardening Guide
I’ve created a hardening guide below that will look at a few key components that administrators will want to make use of in their network.
- Passwords
- LDAP/AD Authentication
- VLAN’s
- 802.1X Authentication
- Disabling Network Ports
- Disabling Unused Services
- MAC Address Filtering
- Physical Access Control
(more…)
Aug 3, 2016
Posted in Encryption, Information Security, News
Russia and the Encrypted World
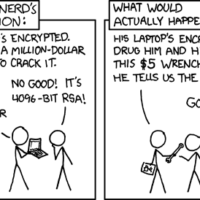
So in top news many have probably already heard of Russia claiming or at least pushing to break encryption.
The initiative is to push for a wide ranging surveillance law, which would allow them access to a whole heck lot of information.
The law calls for metadata and content to be stored for at least six months, plus access to encrypted services.
This means that they also want access to decrypt Whatsapp conversations/chats, Viber & Skype calls… etc… etc…
So how do they go about this now? (more…)
Jul 16, 2016
Posted in Breaches, Information Security, News
Teamviewer is a fairly popular application used to gain remote access to machines.
Many use it to help other users troubleshoot their computer issues.
I personally avoid these types of applications as there are added security risks and concerns.
Teamviewer went down about a month ago which impacted every Teamviewer user on a global scale.
Many people at that time thought Teamviewer had been breached or hacked.
I was alerted about the issue through a friend the same day.
The twitter feed for teamviewer was hit hard by angry users. And as I started to noticed right away many businesses rely heavily on TeamViewer to run their day to day operations. (more…)














 My name is Harry Taheem
I am a Cyber Security Engineer.
My aim is to post things I learn or find interesting and allow others to hopefully gain some more insight. I also plan on posting general IT related issues, as I’d like
My name is Harry Taheem
I am a Cyber Security Engineer.
My aim is to post things I learn or find interesting and allow others to hopefully gain some more insight. I also plan on posting general IT related issues, as I’d like 