Dec 6, 2019
Stealing Windows Wi-Fi WPA2-PSK Passwords through PowerShell
Stealing Windows Wi-Fi WPA2-PSK Passwords through PowerShell
This week, I was hanging out with a friends, who happened to forget their Wi-Fi Password to connect a new device to their network. I decided, I would find a way and help them out so they could obtain the Wi-Fi password. It then led me to a thought, that a malicious attacker could technically use the same technique. Or, that it could be a good technique used when pen testing an environment. So, therefore, I have decided to make a blog post about it. Enjoy!
Why would I want to view the Windows Wi-Fi passwords?
Some people may use this for legit purposes, where they have actually lost and forgotten their Wi-Fi passwords. Or they simply need it in an emergency to connect, and need a method to obtain it right away. Others could use this technique as a good penetration test to see if they also are able to extract Wi-Fi passwords from victim machines. Regardless of your intentions, here is a tutorial on how you can easily obtain Wi-Fi passwords from machines running Windows 7 and Windows 10.
I was able to obtain this information without needing administrator level privileges on the machine.
We can simply use PowerShell commands (2 commands needed to be run) in order to obtain the Wi-Fi passwords.
Let’s get the passwords!
The first command we will use is to get an inventory of the SSID’s/Wi-Fi networks the machines has already connected to and stored the password on.
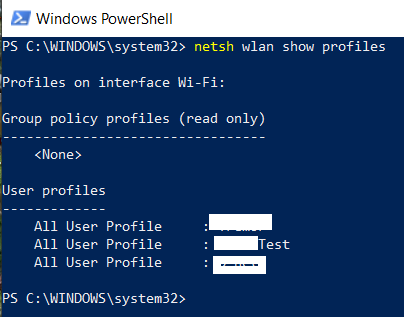
*In my case, I have blurred out the Wi-Fi networks as an added protection for my test machine. But you would see the full name of the Wi-Fi SSID networks.*
The second step now is to target each or a specific SSID to get the password for it.
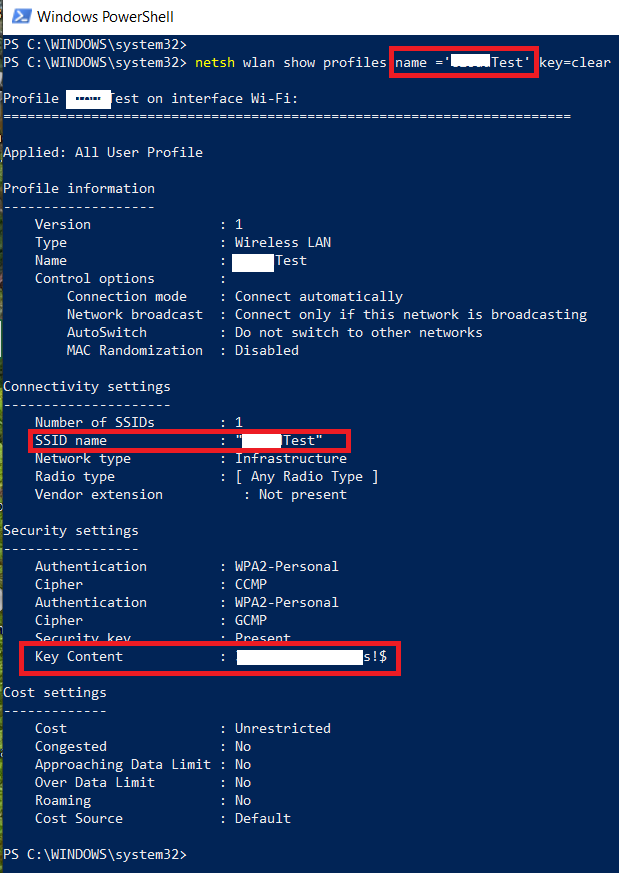
*In my case, I have blurred out the Wi-Fi networks, and password as an added protection for my test machine. But you would see the full name of the Wi-Fi SSID networks and the password.*
The password is stored in the “Key Content” attribute as a value. This is the password for that is being used to connect to this specific Wi-Fi network.
Why use Windows PowerShell over the GUI?
I believe using command line is better as it can get specific passwords for a Wi-Fi network more easily than using the Windows GUI. It also allows you to get passwords when your offline and not connected to a specific Wi-Fi network.
The Windows GUI does have some limited such as: not letting you view passwords unless you are signed into the specific Wi-Fi network.
If your pen testing the best approach to stay silent is to use PowerShell or command prompt shell access. This is assuming you have gotten backdoor access to the Windows machine. And, now are able to run PowerShell commands.
Find this post useful ? List your experiences in the comments section below!











 My name is Harry Taheem
I am a Cyber Security Engineer.
My aim is to post things I learn or find interesting and allow others to hopefully gain some more insight. I also plan on posting general IT related issues, as I’d like
My name is Harry Taheem
I am a Cyber Security Engineer.
My aim is to post things I learn or find interesting and allow others to hopefully gain some more insight. I also plan on posting general IT related issues, as I’d like 
Leave a Reply