Apr 2, 2018
DNSTwist – Domain Phishing Enumeration
DNSTwist – A Look at Domain Phishing Enumeration
A few weeks ago, I happened to stumble upon a tool called DNSTwist. And, like every tool I ever encounter, I always like investigate more into a tools capabilities and what it can offer. After reading more about the tool through another blog I was reading at that time. I was pointed towards the official Github page for DNSTwist. The tool itself is great and something every company should at least look at on a yearly basis. Phishing attacks are on a rise, and the expectation is that they will continue to increase over time. So, I’ve decided to create a very quick tutorial on how to use DNSTwist, and what it can offer for anyone that wants to make use of it. This is a great tool for Pen Testers and Security Analysts!
What can DNSTwist do for me?
I found using this tool gave me great insight into major phishing attacks that could be conducted against users or companies. Now how is this a good thing? Well, if you know the type of attacks that can take place, or how a certain attack can take place. Then, you are better able to find ways to defend against this type of attack. At the minimum, you can at least detect this specific type of attack. In my experience there are more stats revealing that there is now a rise in phishing attacks against companies and users.
So how does this tool help me? Well simply put it, it can help you find domains someone may use to phish your business or company.
For example, if you own mynamehere.com, someone may buy a similar name such as mynamehere.co (note there is no “m” at the end), or use nynamehere.com (note there is a n instead of a m). Many users will fall for this trick, as they miss noticing the m at the end of “.com”, or the “n” in front of mynamehere. Let’s face it, not all of us concentrate on the email address in such detail as most people tend to just skim through emails. What happens when someone innocently skims through an email and misses the domain name? And, they click on a phishing link? That leads to a whole new level of issues. So, let me show you how you can use this tool to help strengthen your security posture.
How do I use it?
I’ve listed a simple tutorial below using Stealthbay.com as an example. I would suggest you test this with all of your business and personal domain names.
I used Kali in my example, but you could use any Linux OS to make use of DNSTwist.
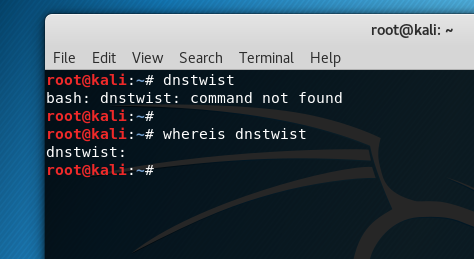
In Kali, DNSTwist is not an application which comes pre-installed, nor will most Linux systems with their default packages. So, in my case I had to install it via the github repo.
Download Libraries/Packages
But before, I can download DNSTwist, there will be a few packages and libraries most machines will need.
I’ve listed them below in my screenshot.
Please download and install these prior to working with DNSTwist.
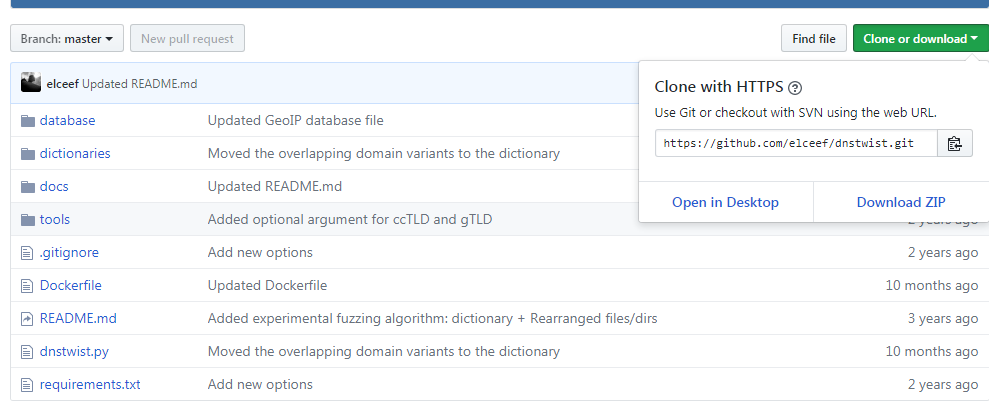
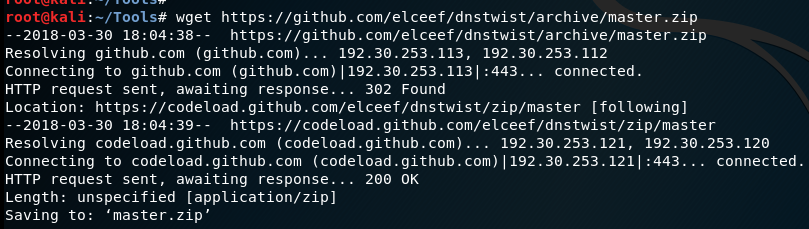
After the libraries and packages have been installed on your machine. Go ahead and download DNSTwist from the github repo as shown below in the screenshot.
Download DNSTwist
Download and extract the DNSTwist files on to your system.
Running the search
Next, we can now run DNSTwist, and I’ve broken this down to 2 types of searches.
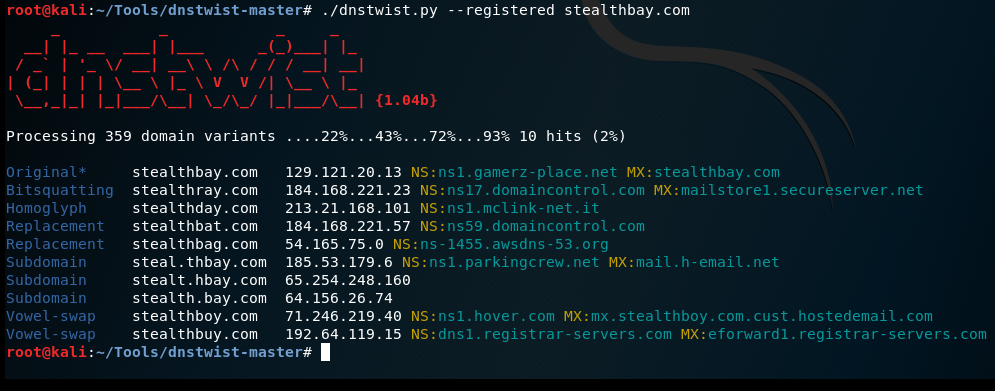
The first search is for ALL possible domains, while the second search lists out any domain that is registered which matches closely to Stealthbay.com
In the screenshot below, you can see that the script runs through various types of domain checks. In the 1st section it looks at adding or concatenating letters with a domain name. Then, looking it up to see if the domain exists and/or is registered.
Note – There is a command that can be used to find the IP Address of the server if the domain is valid and is hosting a website. I have not listed it in my screenshots, but the github page has further commands that can be run with DNSTwist.
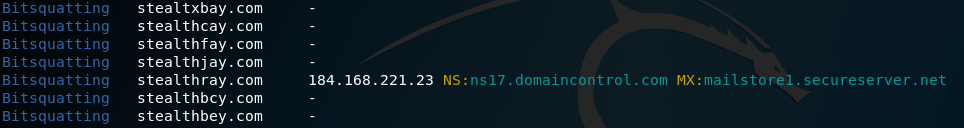
As the scan goes through, it also looks at bitsquatting domain names. Bitsquatting refers to the registration of a domain names one bit different than a popular domain. In my case it did find a domain name called stealthray.com. Fortunetly for me this domain name and website are no threat to Stealthbay.
Listing Registered Domains
In the screenshot below, we can see a list of all domains registered. These are the domains we need to worry about, which could closely resembles Stealthbay.com
Now, in my case most of these domains are harmless to Stealthbay. However, the results will differ for much larger websites, or businesses where targeting them would possibly yield a higher risk. I purposely haven’t checked amazon, Microsoft, etc… as this tutorial is for educational purposes. And, no attempt is made to attack an organization or business.
But, the results for more popular sites will show how many domains are actually registered out there. Remember, if you search other websites it’s due AT YOUR OWN RISK.
Summary
I hope this tutorial shows why it is very important to search for similar domain names, and ones that especially resemble close to your own brand name. Cyber Criminals are using domain phishing as a large source for phishing email and other phishing attacks. Remember, humans make mistakes, and all it takes is one simple click in an email to give a cyber criminal access to your computer and systems.
Credits
DNSTwist is a tool created by Marcin Ulikowski.
The github repo can be found here –> https://github.com/elceef/dnstwist













 My name is Harry Taheem
I am a Cyber Security Engineer.
My aim is to post things I learn or find interesting and allow others to hopefully gain some more insight. I also plan on posting general IT related issues, as I’d like
My name is Harry Taheem
I am a Cyber Security Engineer.
My aim is to post things I learn or find interesting and allow others to hopefully gain some more insight. I also plan on posting general IT related issues, as I’d like 
Leave a Reply