Apr 24, 2017
BurpSuite & ZAP Bypass Proxy
BurpSuite & ZAP Bypass Proxy
I wanted to make this tutorial for users that might get stuck in a similar situation.
I was security testing a website using Burpsuite and would end up with SSL Handshake failures. And, it really made no sense at first since Burpsuite uses Java. And, I had the latest version of Java installed on my machine. Burpsuite was giving me SSL Handshake failure alerts and was asking me to install JCE Strong Cipher policies. Turns out the website was using VERY strong ciphers (which is a very good thing). And, they were using no medium or outdated ciphers.
Now, these ciphers are so strong that even the latest Java package does not contain them….yet.
So that meant I had to find another way to use Burpsuite, but still have the ability to make a proper SSL handshake using the strong ciphers. I then turned to another similar product called OWASP ZAP. This is a great product and I have used it back when I didn’t quite have the funds to purchase Burpsuite. What I realized was that I could use Burpsuite and have ZAP filter my traffic for me. For some reason ZAP has all of the strong ciphers and did not fail the SSL handshake, which meant I could transfer traffic as:
Browser -> Burpsuite -> ZAP -> Webserver
The downside to this was that I noticed my scanning speed has decreased quite a bit compared to just scanning with Burpsuite alone. And, this might be expected since additional tools and resources are now be allocated and used for the scan.
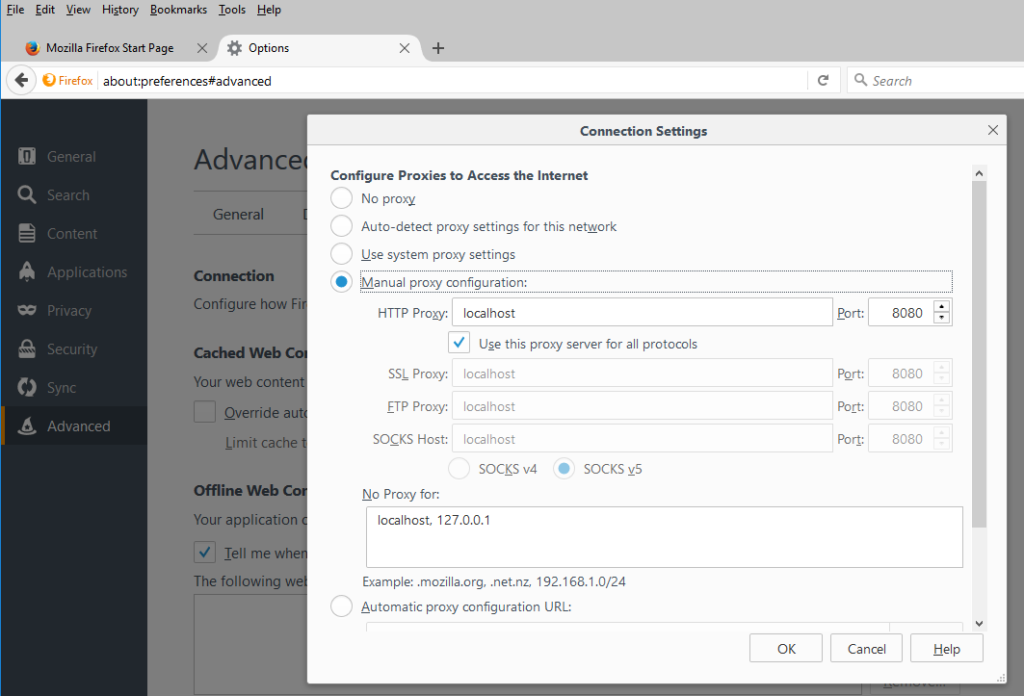
Setting Up The Browser
First things first, my browser used for security testing is Firefox, as they seem to have the best apps for pen testers. The Network settings in Options -> Advanced -> Network need to be changed. We want to point all traffic to Burpsuite, so the HTTP Proxy setting should be set to localhost or 127.0.0.1, and set the port to 8080. Be sure this is set for ALL protocols, you can tick the use this for all protocols button to do so. Confirm the settings and now all traffic in the browser will flow through Burpsuite.
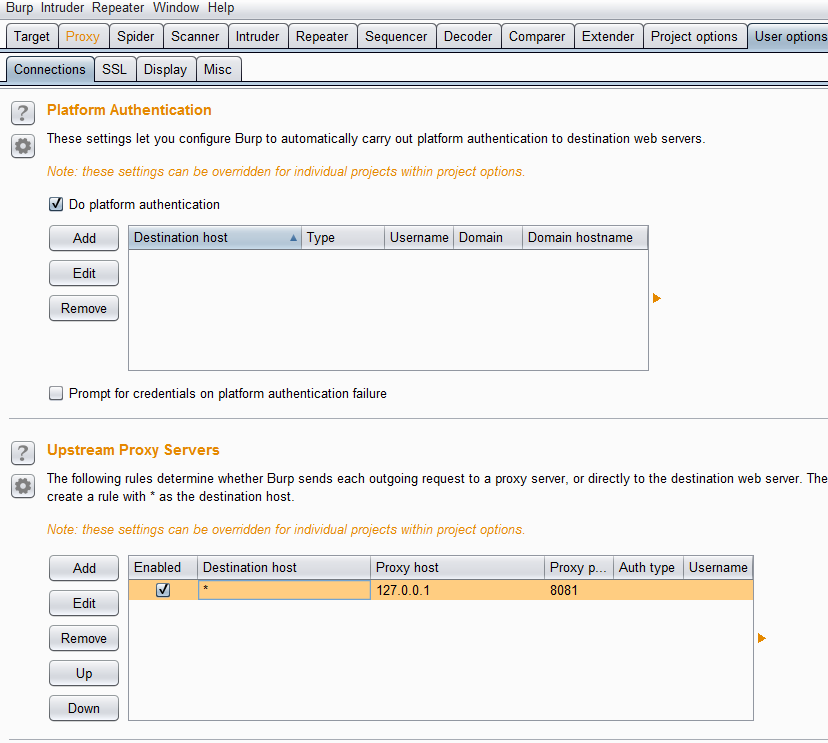
Setting Up BurpSuite
Fire up Burpsuite and create a new project. Use the User Options Tab -> Connections -> Upstream Proxy Servers. The settings for OWASP ZAP need to be specified here. Add a new upstream proxy for all (wildcard – *) sites and point it to 127.0.0.1, but this time we will add a new port of 8081. So why have we added a new port? Well, we can’t have traffic on the same port for both applications on the same port and host. So what we have now done is created traffic on one port, which is sent off to another port.
An example would be 127.0.0.1:8080 (Burpsuite) -> 127.0.0.1:8081 (ZAP) -> WebServer (www.randomsite.com) The port change is just another way to transfer traffic from one application to another without mixing the connections as one. Otherwise, traffic would hit both apps at once and not going through one and than get forwarded to the other.
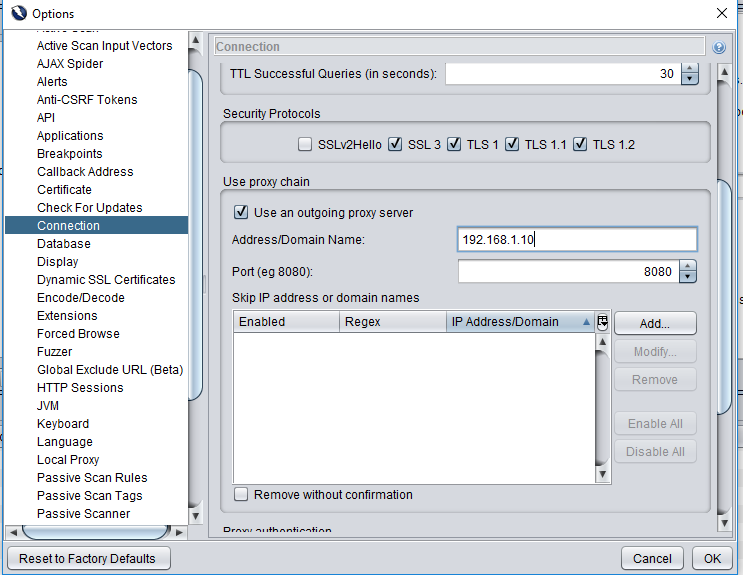
Setting Up OWASP ZAP
Things get a bit more complicated for ZAP since we need to tell it to ACCEPT data from Burpsuite. And, we also need to let ZAP know how it can get out to the Webserver/Internet. So to start off we will setup the way out. In my case the firewall and proxy server that let you out is 192.168.1.10. We will set this up in the Options tab -> Connection. Enter in your IP address to get out to the Internet or external Webserver.
The final step left is to let ZAP know how Burpsuite will send data to it. This can be setup in the Options Tab -> Local Proxy. Here we will use our localhost IP 127.0.0.1 and port 8081. And, that’s it! Now when any website is browsed via Firefox, the data will go through Burpsuite and then ZAP. This will allow Burpsuite to make SSL handshakes via ZAP so there should be no more SSL handshake failures.
Hopefully this tutorial helps people out there.
Enjoy and good luck!












 My name is Harry Taheem
I am a Cyber Security Engineer.
My aim is to post things I learn or find interesting and allow others to hopefully gain some more insight. I also plan on posting general IT related issues, as I’d like
My name is Harry Taheem
I am a Cyber Security Engineer.
My aim is to post things I learn or find interesting and allow others to hopefully gain some more insight. I also plan on posting general IT related issues, as I’d like 
Gracias y un saludo